The Second Brain After Three Months
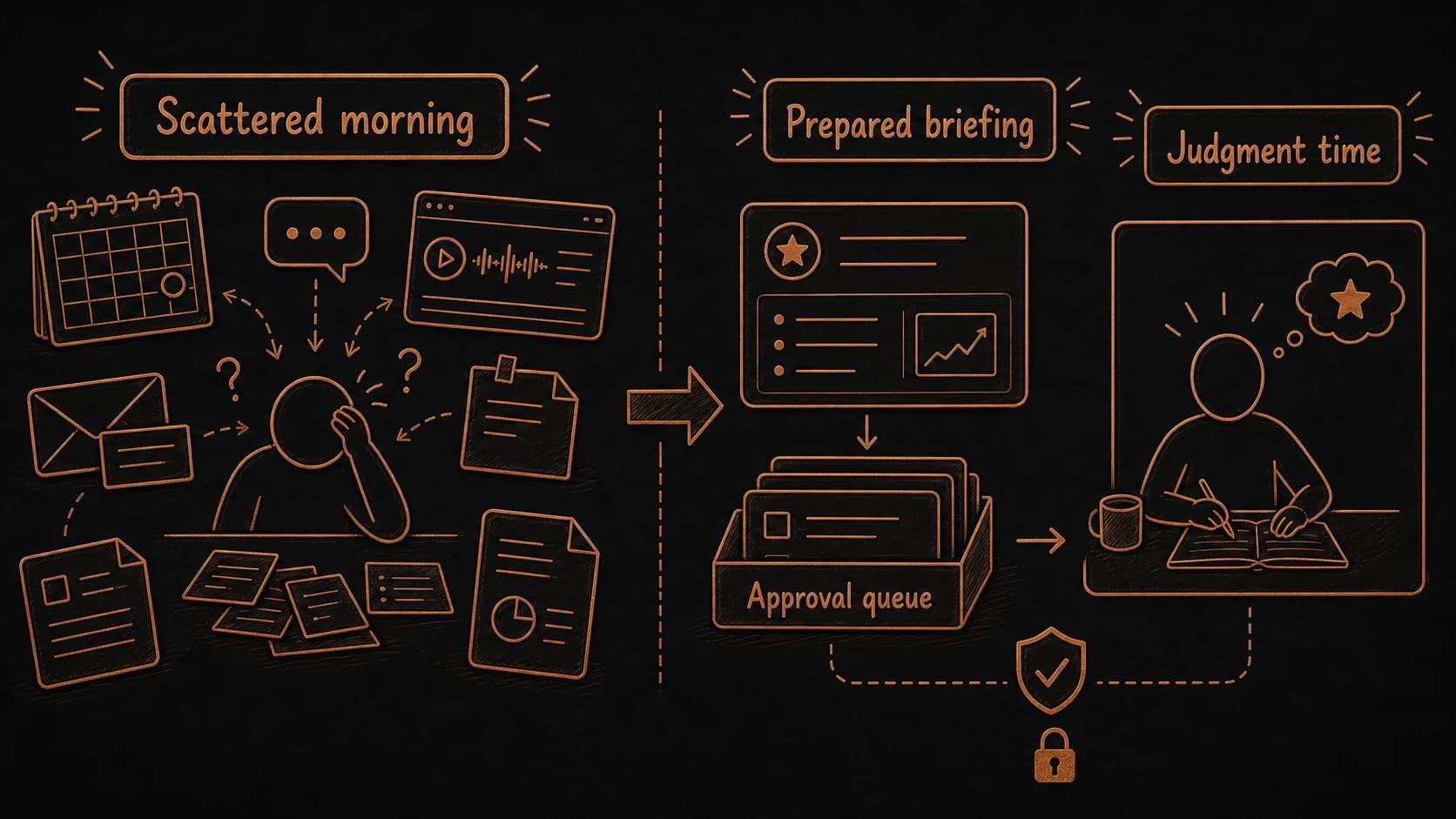
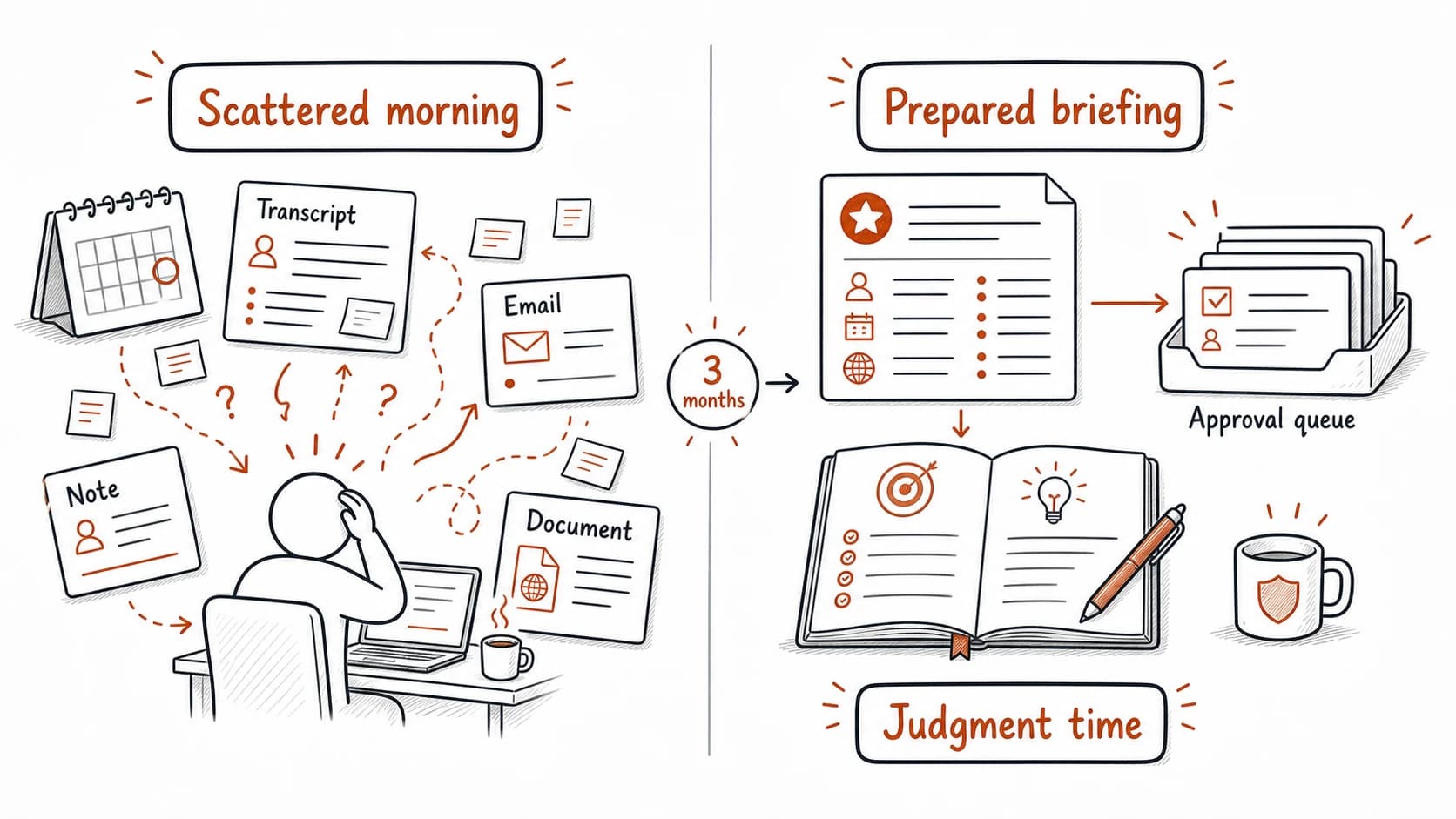
Use case: the Thursday call after three months
The book opened with a scattered morning. You had 20 minutes before a client call, and the you needed lived in five places: the calendar event, the meeting from last week, an email thread with a changed deadline, a voice note recorded on the way home, and a planning document you updated three days ago. You searched your email, scrolled through your notes app, opened the calendar, scanned the document, and rebuilt context from memory. You walked into the call prepared enough to avoid embarrassment, with no time left to think about what you wanted from the conversation.
Three months later, the same call arrives. The surfaced the from last week, the updated pilot scope from the email thread, Renee's confirmed Friday , and the compliance dependency the layer discovered across two projects. The overdue follow-up with the legal team appeared in the approval queue. You opened the briefing, verified one , approved the follow-up message, and spent the remaining 15 minutes thinking about what you wanted the conversation to accomplish. The was there. The preparation happened before you sat down.
The difference is worth naming precisely. The opening chapter asked you to name one recurring situation where scattered costs you time. The Thursday call was that situation. Every chapter since has added one working piece, and the call now runs on the system you built. The system did not make you smarter. It freed the time you used to spend reconstructing context and redirected it toward the kind of thinking that requires context to be present: deciding, connecting, evaluating, and following through.
Every concept in this book works together in one loop
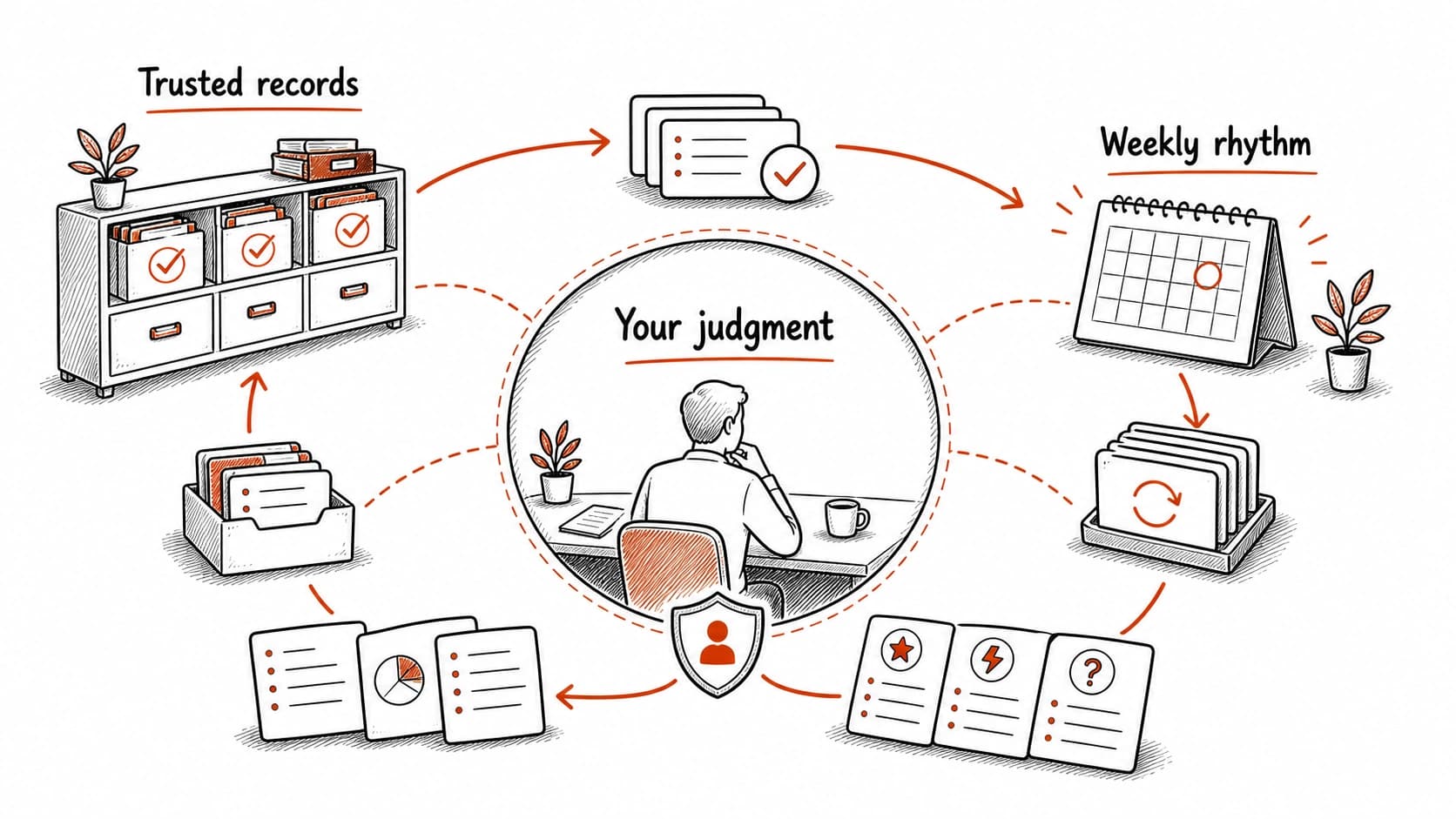
Trust states started as a binary distinction in the privacy chapter: raw sources carry risk; reviewed records carry approval. By the time you reached , trust had become a multi-layered question. A raw source can be promoted. A can go stale. Two trustworthy records can disagree. And the synthesis report that interprets them needs its own verification before it becomes the basis for action.
Source trails started as a link back to one original. By the time the arrived, source trails were the only evidence that a scheduled finding was grounded. A briefing item without a citation is a system-generated opinion. A briefing item with three independent sources and a confidence level is knowledge you can act on.
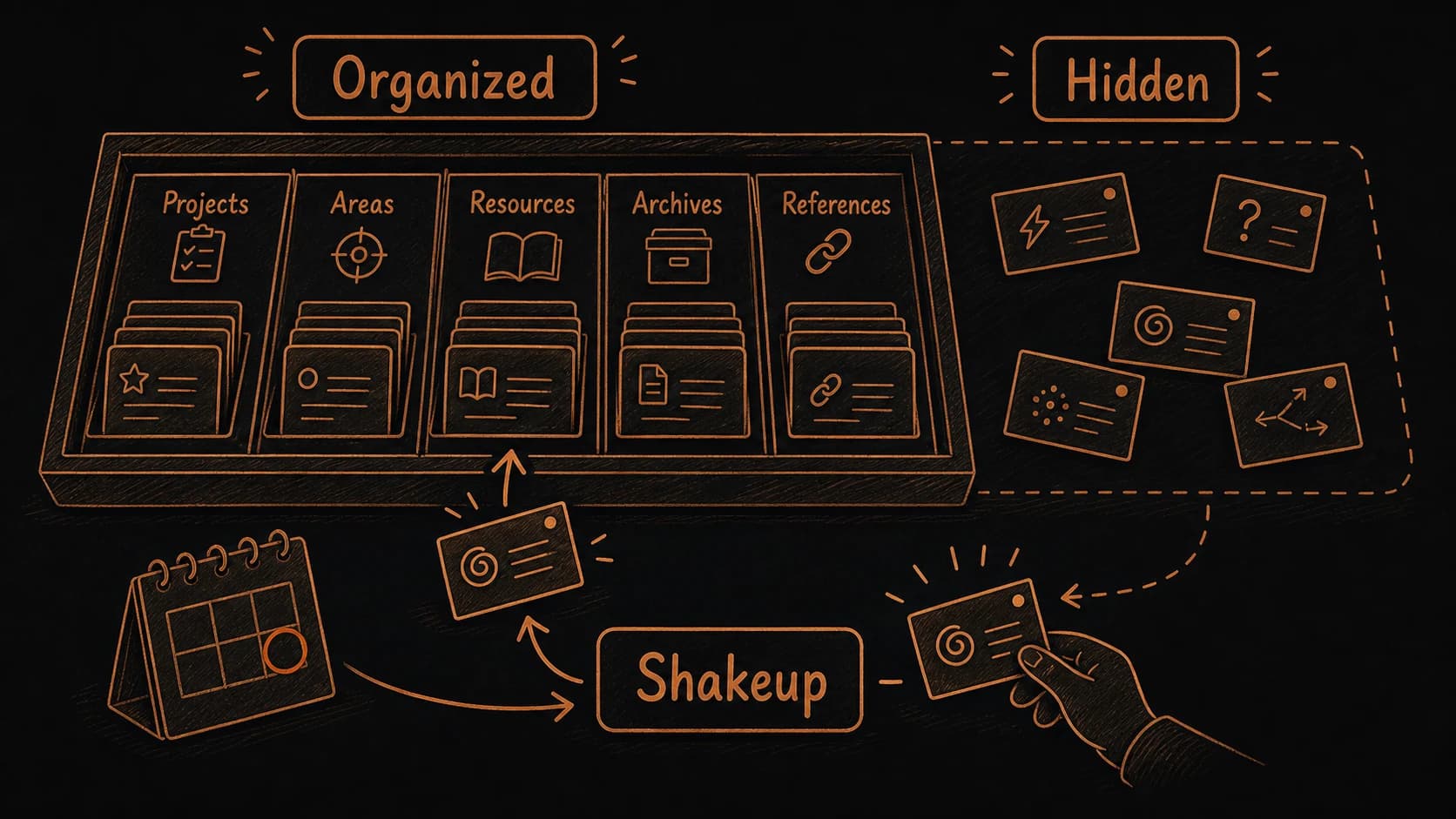
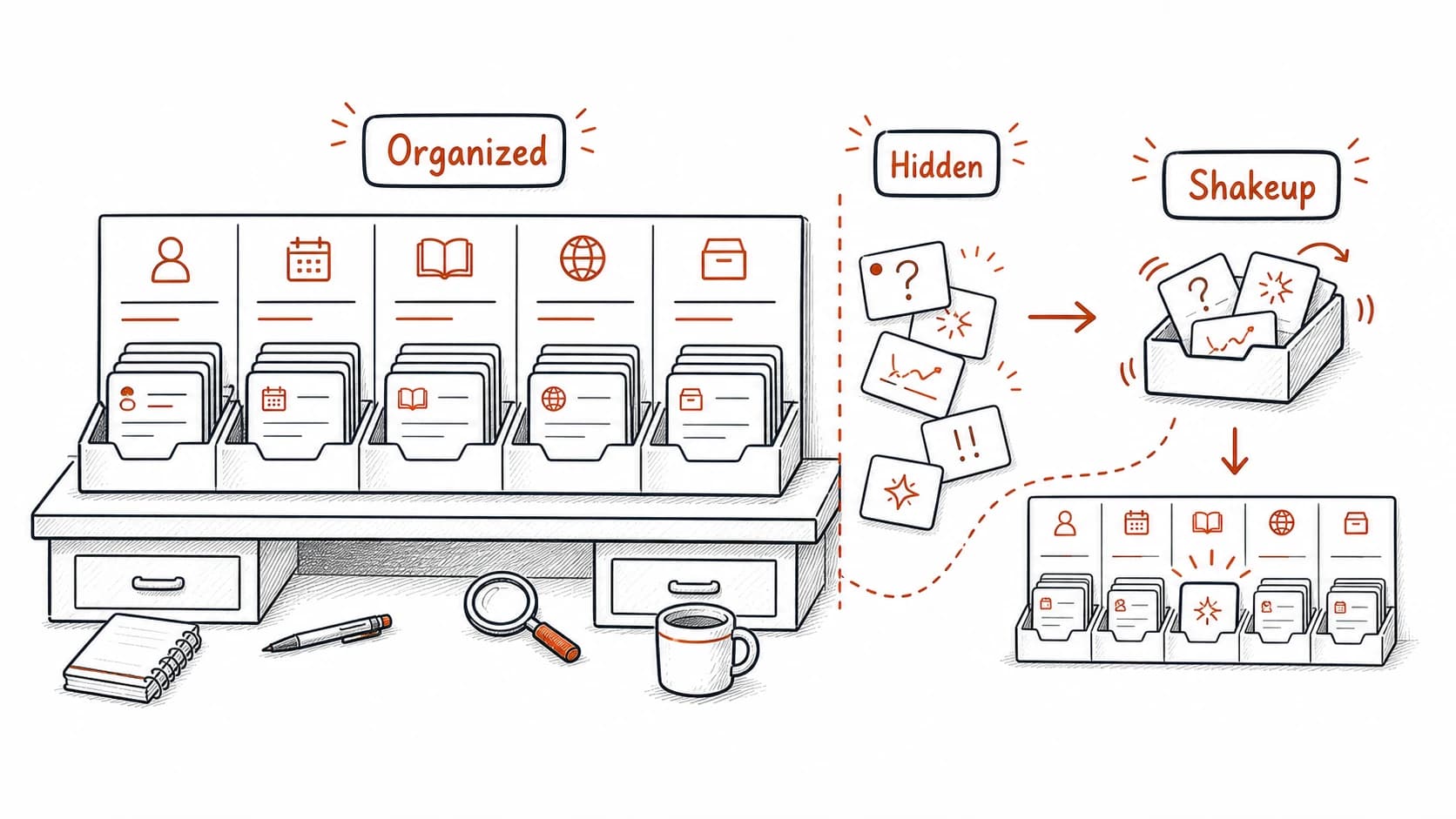
keeps your material sorted by use: Projects for active work, Areas for ongoing responsibilities, Resources for reusable reference, Archives for completed history. describes what you do with that material along the way: Capture the raw source, Organize it into a project with , Distill the decisions and commitments from the evidence, Express the result as a task, message, brief, or published artifact. Together, they form the full loop from scattered source to approved action.
The keeps the loop alive. Capture without review fills the until you stop trusting it. Review without misses the connections across records. Synthesis without scheduling requires you to remember to run it. Scheduling without source boundaries produces noise. Each part of the system depends on the others, and the weekly review is the checkpoint that confirms they still work together.
When the system becomes a constraint on your thinking
The most important trust question the book has not yet asked is about the system itself. After three months, your has accumulated structure: project labels, categories, trust states, source trails, patterns, scheduled runs. That structure helps you find what you need and verify what you find. It also creates a frame that filters what you notice.
A well-maintained system surfaces the connections its structure can see. A linked to a project will appear in the project view. A compliance note tagged with the right topic will show up in . An untagged insight scribbled on a napkin and dropped into the may never surface, because the structure has no path to reach it. The is excellent at finding what you organized. It is less reliable at surfacing what does not fit the categories you built.
The fix is to shake things up on purpose. Once a quarter, browse the without a question. Read old records outside their project . Ask the layer to compare sources that have nothing obvious in common. The system is a tool for thinking, and thinking sometimes requires breaking the frame that makes the tool efficient. You are the authority over the system, including the authority to question whether its structure still serves you.
What the system does not do
The does not think for you. It preserves , surfaces connections, and proposes follow-through. The judgment about what matters, which connections are meaningful, and which follow-through is worth pursuing remains yours. If you delegate that judgment to the system by accepting every finding and approving every proposed task, you have replaced your thinking with the system's interpretation of your records.
The system does not handle ambiguity well. Source trails work best when the source is a document, an email, or a with a clear date and author. They work less well with informal conversations, half-formed ideas, and intuitions that resist being captured in a record. Some of the most valuable things you know will never have a source link.
The system does not scale infinitely. A with 200 well-maintained records is more useful than one with 2,000 records that were captured and never reviewed. If the consistently takes longer than 45 minutes, or if the scheduled output produces more noise than insight, the system has grown past the point where maintenance effort returns value. The response is to simplify: archive aggressively, reduce the number of active projects, narrow the source boundary, and let the system serve fewer things well.
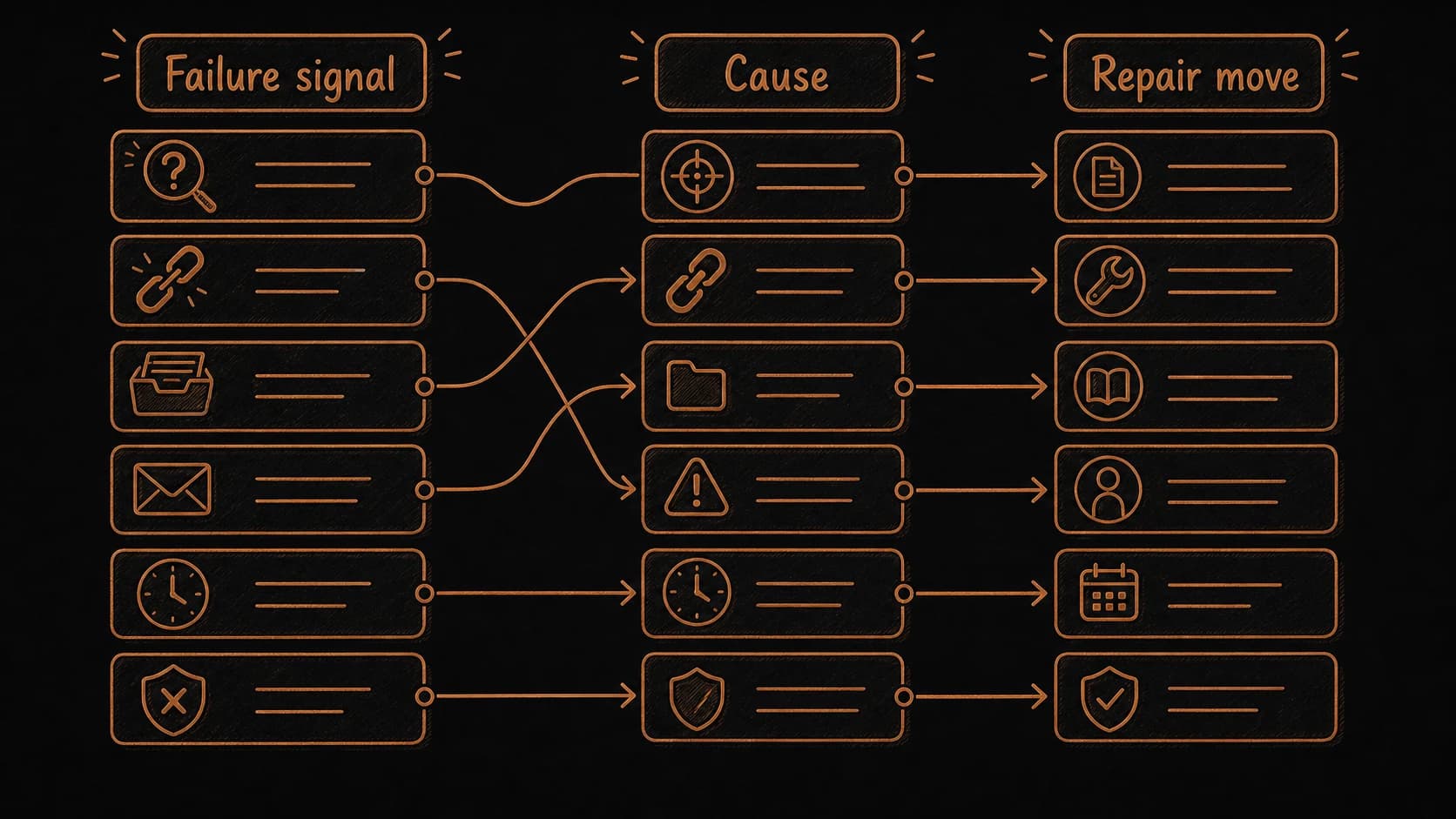
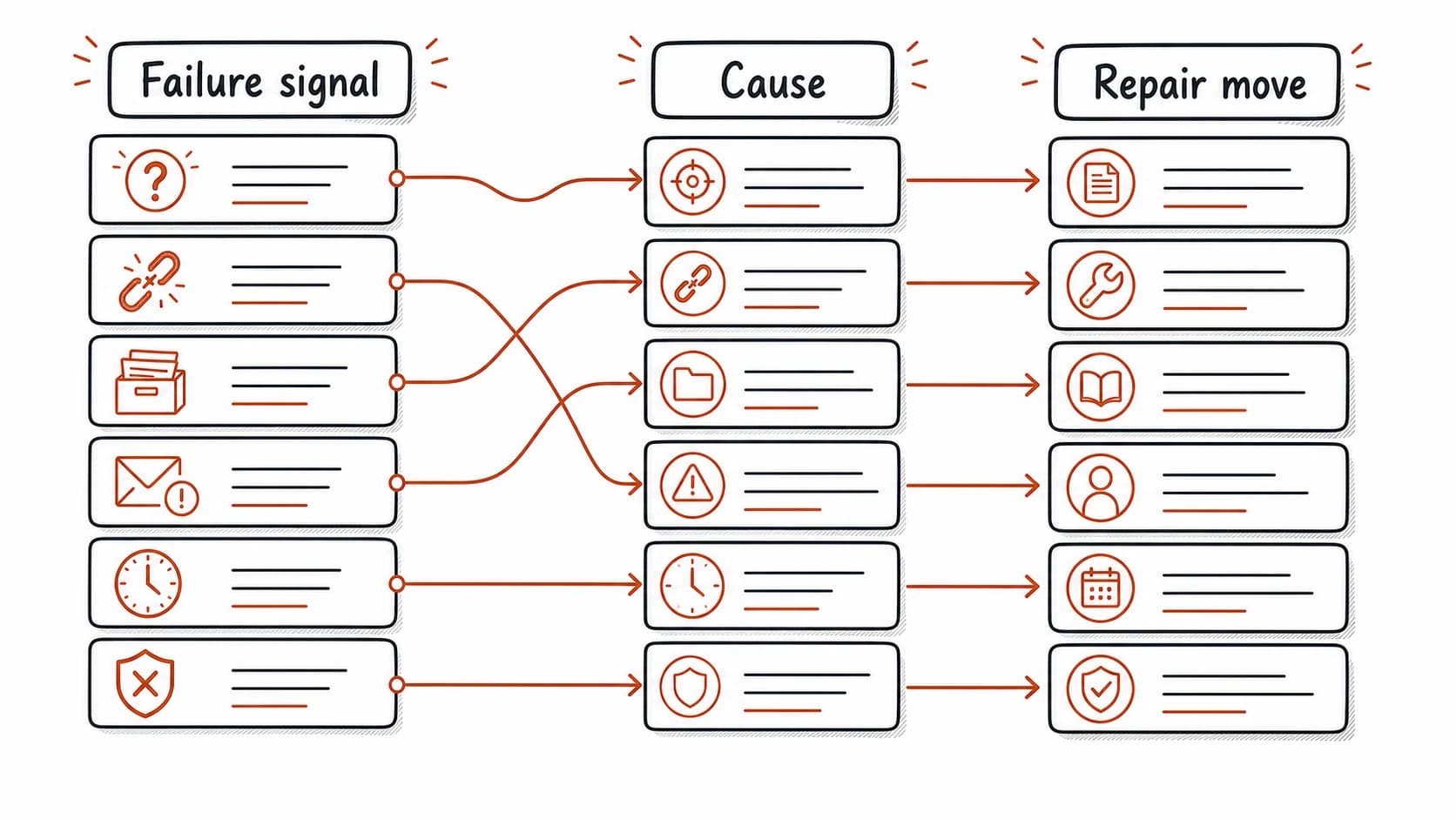
When the system breaks, the failure points back to one chapter
Every failure mode in this book has a repair move and a chapter where the skill was introduced. When something goes wrong, the table below tells you where to look and what to fix. Most repairs take less time than the problem they prevent.
You can design workflows the book did not cover
Every chapter before this one covered a specific step in that path: capture, connect, build, retrieve, act, track, review, repair, synthesize, map, and schedule. Your work will produce situations the book did not anticipate. A hiring process, a research project, a personal health decision, a creative collaboration, a financial review. Each one involves , trust decisions, and follow-through, but the specific sources and review questions will differ.
You now have the components to design your own workflow for any situation that fits the pattern. Start with the : what will you capture, and what privacy label does it need? Define the trust states: what counts as raw, what counts as reviewed, and what review question separates them? Build the test: what question should the system be able to answer, and what source should it cite? Establish the review rhythm: how often does this material go stale, and what check catches the drift? Design the pass: what connections across these records would change your next move?
The prompt template below guides this design process. Use it when you encounter a new situation that your current system does not serve, and you want to extend the to cover it.
Design a second-brain workflow for a new situation
Claude interviews you about a new situation and designs a capture-to-action workflow using the architecture you already built.
The reader as architect
This book began with a promise: your mind does its best work when it can notice, judge, connect, and create without spending its energy on remembering where things are. The handles the remembering. The handles the maintenance. The layer handles the connections across records. The scheduled briefing handles the preparation.
What remains is the work that only you can do. Deciding which pattern matters. Judging whether a is real or tentative. Noticing the insight that does not fit the categories. Following through on what you chose to pursue. The system supports this work by keeping the present, the sources traceable, and the follow-through visible. The thinking is yours.
The system will evolve as new source types appear and tools change, and the will catch what drifts. The approval boundary started as a privacy rule: the assistant holds any action that would move content across access levels. It became an approval queue: decisions, tasks, and messages waiting for your sign-off. It gained stop conditions: automated runs that pause when they encounter conflicts or unclear sources. Each stage gave you more control over what the system may do on its own.
You now own the architecture: the trust hierarchy, the , the , the layer, and the approval boundary. These five pieces are transferable. They work regardless of which tool you use, which AI model you choose, or how the technology changes. The architecture is yours. Build with it.